Our smartphones have become indispensable and, as such, attackers are targeting them with increasing frequency and sophistication. With the recent rapid rise in smartphone targeted attacks, the new year may just be the time to clean out your phone and make sure you haven’t picked up any adware, spyware, or malware.
First order of business: if you haven’t restarted your phone recently, I recommend doing so soon and regularly thereafter. Much of the malware that affects smartphones stays in memory to avoid detection. This means that it can’t survive a reboot, so it’s a good way to clean out the cobwebs. To make this even more effective, download the latest update for your device first, so you reboot with the latest and greatest software available for your device.
Now, look at your settings. There are a substantial number of important settings that you might want to look at. I highly recommend taking some time, especially for your most used apps, to understand their settings and permissions (ever wonder why your 3rd party calculator app needs access to your location?). There are a few areas to prioritize here:
• Navigate into your VPN settings and see if you have any profiles installed. While most VPNs are useful security tools, malicious VPNs were extremely popular not-too-long ago and can expose all your traffic to an attacker or grant them access to your device.
• Look at the Bluetooth devices and connections. Unfamiliar entries could be malicious and expose your device to an attacker or send recordings to a remote user.
• Check installed keyboards. Third-party keyboards can send your keystrokes and other data to remote servers regardless of the app you’re using.
• Check whether developer mode has been enabled. On iOS, this allows unsigned applications to be installed, including malware, spyware, or tracking tools.
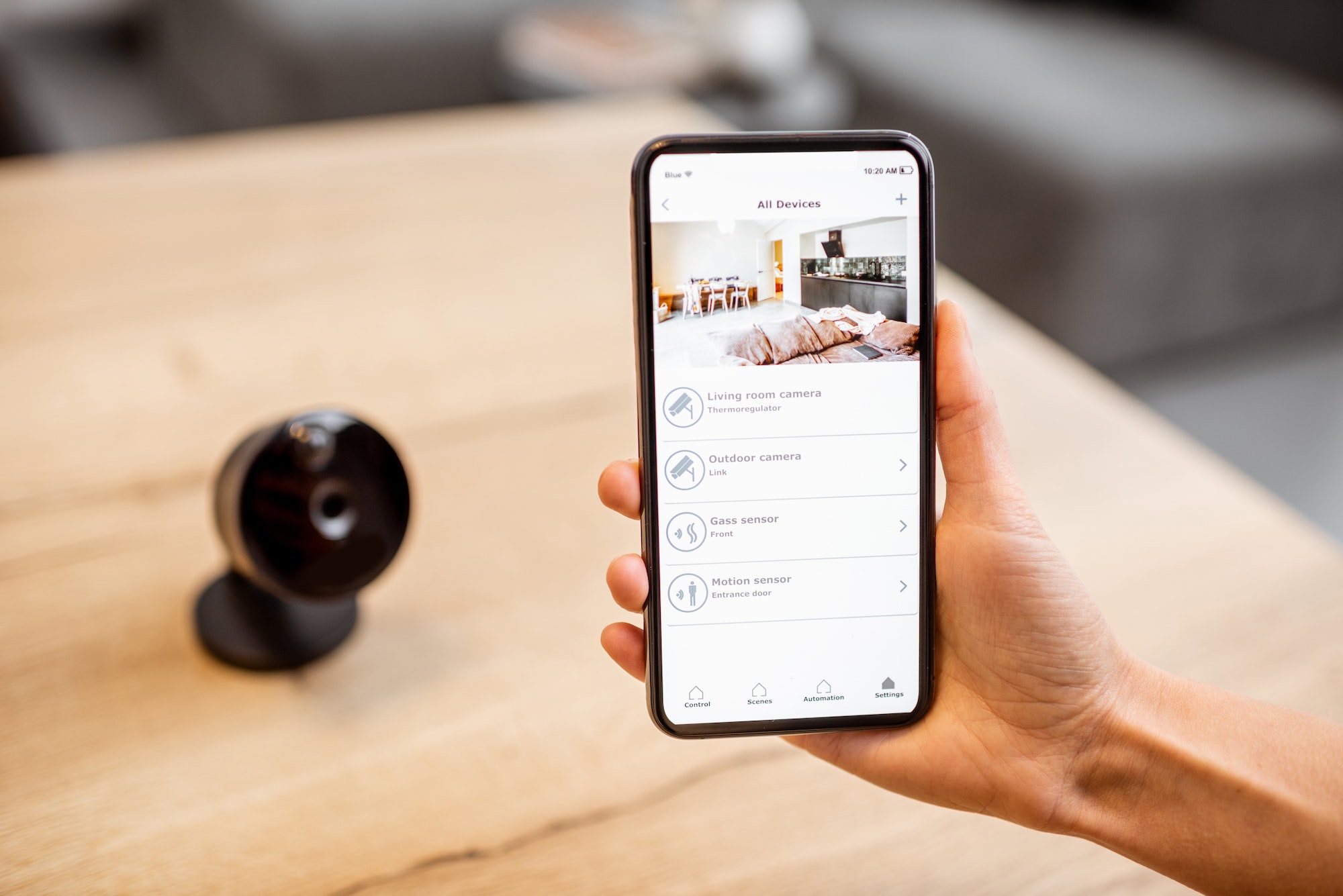
• Social Media – check to see what permissions you’ve given to social apps, dating apps, and other frequently accessed applications. They can retain control of the camera, microphone, and other components long after you have switched to another app.
Now, look at the apps themselves. The average smartphone user has over 100 apps installed on their device and that number continues to grow. And most users rarely delete apps even if they stop using them (there are even apps to help you find unused apps and subscriptions you’ve forgotten about!)
• See an app you don’t remember installing? Before you open it to check it out, do a quick search for the app name. It could be malware or spyware – especially if you’ve jailbroken or allowed side-loaded apps and third-party app stores on your phone. Some malicious apps can load an app icon and wait for you to open it, thus infecting your device.
• See a familiar app with a new icon? Instead of a rebrand, it might be an imposter. While the app stores try to prevent this, there are many cases where these duplicates get through and may be loaded with unwanted capabilities.
• Check the lists of popular iPhone tracking and spyware apps (e.g., 10 Best Spy Apps for iPhone in 2022) and see if any of them appear anywhere on your device. Many of them are marketed as parental control software, but they have powerful monitoring and tracking capabilities that can be used by a malicious actor. (Please note that these apps are designed to avoid detection. If you suspect one of these apps may be installed, you should wipe your phone and reinstall your apps individually – NOT restore from backup).
• Delete old apps that you don’t use. Not only will it free up space, but you’ll also get rid of any tracking or excessive permissions you granted the app when you used it frequently.
After that, look at your cloud accounts (Google, iCloud, O365, etc.) and recognize all the signed-in devices. In some cases, that list can be long, especially if, like me, you have had them for a long time and many generations of devices. You can sign out all signed-in accounts and reset your password, then make sure you only allow devices you know. Enable two-factor authentication as well if you haven’t already. Some malware gains access to your phone via the cloud APIs these services provide, so make sure you protect them with the same vigor as your phone.
To really start over from a clean slate, perform a factory reset and install apps directly from the app store. Note that if you restore from backup, you are potentially reinstalling any spyware you had before (this may mean losing old texts, voicemails, etc.):
• Apple: Restore your iPhone, iPad, or iPod to factory settings
• Android: Reset your Android device to factory settings – Android Help
Finally, another way that malicious actors can attack your phone is by SIM swapping or cloning. Your SIM card identifies your phone to the network so it can route calls and texts properly. By cloning your SIM, an attacker could receive a copy of every call or text sent to your phone. SIM Swapping has been used widely to defeat text-based 2FA (2 Factor Authentication) on banking and other sites by causing those authenticator codes to go to the bad guy instead of you.
It can be hard to detect because it’s not directly attacking your device but being on the lookout for odd behavior like suddenly not receiving phone calls or text messages or receiving authentication texts from your account holders like your bank can be indicators of a SIM attack. One way to try and avoid these attacks is to avoid using SMS or text for 2FA/MFA whenever possible and contact your mobile service provider and ask what safeguards they have that they can put in place to protect you from these attacks, like a PIN used for transactions with the mobile service provider for authentication.
Your phone knows pretty much everything about you, and hopefully, these tips have shown you that it’s worth protecting while giving you some practical ways to do so. Start the year with a clean slate by making sure your device isn’t spying on you!